What We Do
Comprehensive protection,
practically delivered
We cover every critical layer of your business cybersecurity, implemented, managed, and explained in plain English.

Multi-factor authentication (MFA)
Implement MFA across all business systems and remote access points. Requiring more than just a password dramatically reduces the risk of account takeovers, even if credentials are compromised.

Endpoint protection
Deploy modern EDR solutions capable of detecting ransomware, malware, and suspicious behaviour before they spread. Centrally managed so every device stays consistently protected.

Security awareness training
Regular training and phishing simulations for your team. Human error drives the majority of breaches, educated staff are your first and most effective line of defence.
Patch management
Automated patching across all systems, browsers, and third-party applications. Consistent updates close the known vulnerabilities attackers rely on most.

Secure configuration & Access controls
Enforce least-privilege access and secure configurations across your environment. Conditional access policies and secure admin controls protect cloud apps and remote users.

Incident response & Recovery planning
A tested incident response plan and regularly verified backups, including off-site and immutable copies, so you can recover fast when the worst happens.
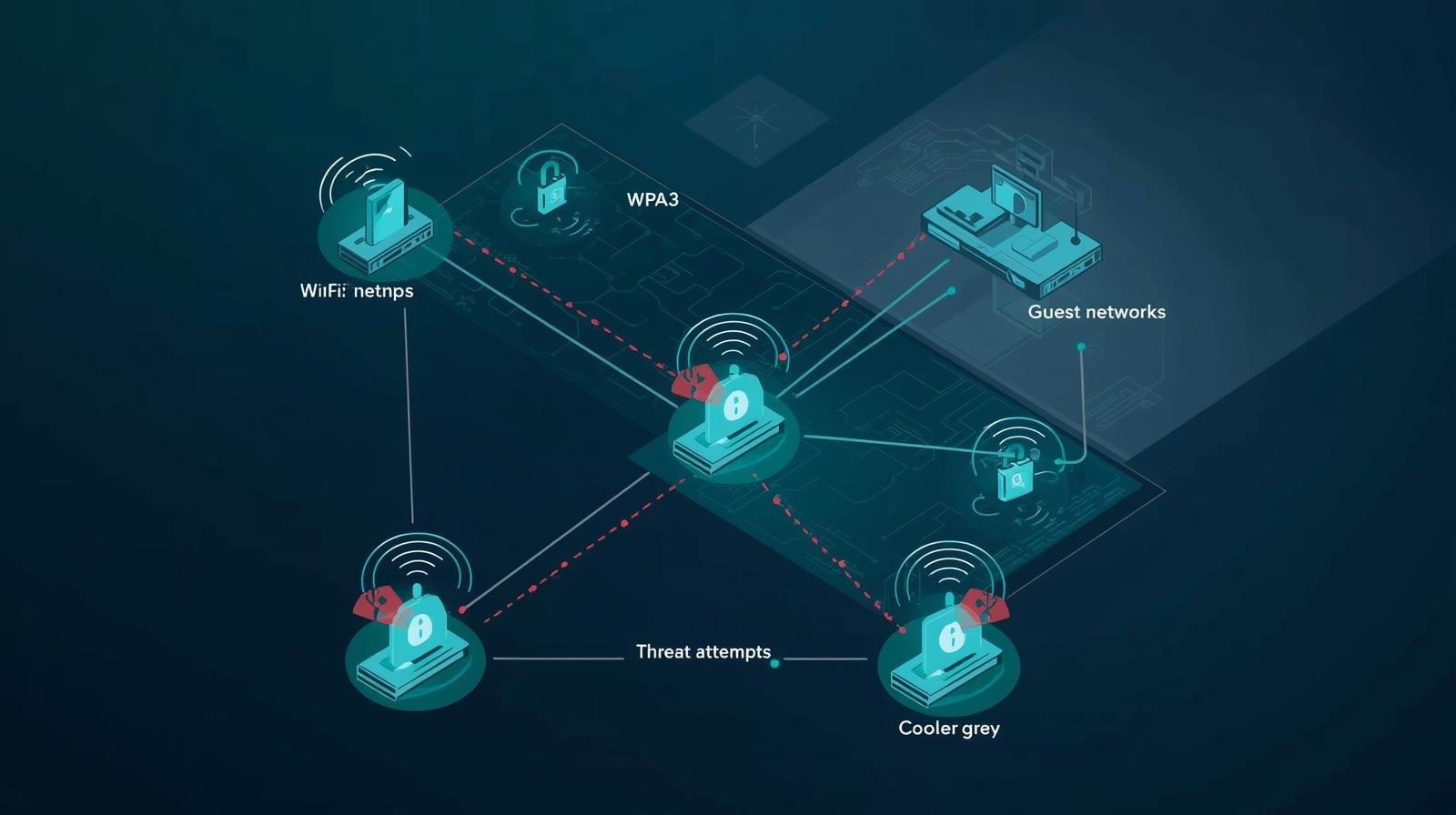
Network security
Modern firewalls, WPA3 Wi-Fi authentication, segmented guest networks, and network architecture that contains threats and stops lateral movement.

Vulnerability management
Structured, risk-prioritised vulnerability assessment and remediation. Automated scanning reduces the time from discovery to fix, closing windows before attackers find them.
Efficiency through automation
Eliminate manual, repetitive tasks with intelligent automation. Automated patch deployment, scheduled reporting, and consistent workflows free your team while improving your security posture.